Phone Verification Hub Check Spam Phone Number Revealing Trusted Data
A Phone Verification Hub aggregates signals from trusted sources to assess whether a phone number is legitimate or spam. It cross-references calling patterns, metadata, and behavioral fingerprints, then presents aggregated, anonymized indicators to protect individual privacy. The approach emphasizes data minimization and privacy-by-design, with transparent summaries of use and consent-driven policies. It provides verifiable provenance without exposing personal details, inviting scrutiny from stakeholders while inviting further consideration of how trusted data shapes outcomes.
What a Phone Verification Hub Is and Why It Matters
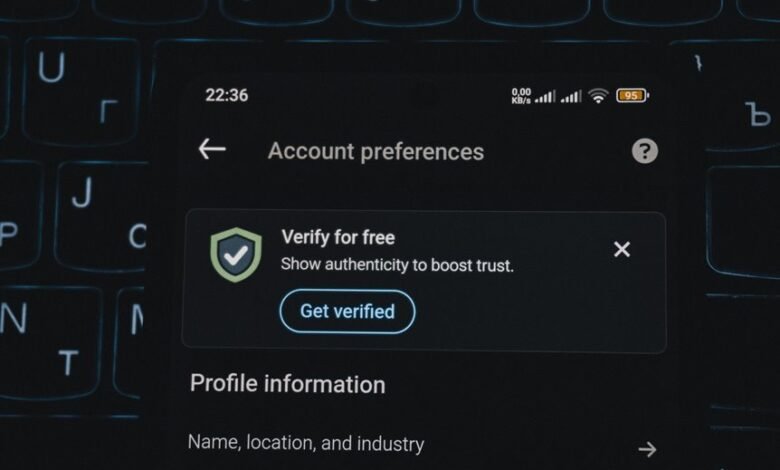
A phone verification hub is a centralized service that aggregates, analyzes, and validates phone-number data to confirm user identities and detect fraudulent activity.
What is verification, and why it matters, emerges from cross-validated signals, consented data, and rigorous governance.
How verification hubs work relies on layered checks and privacy-by-design.
Why trust matters rests on transparency, accuracy, and verifiable provenance.
How to Spot Spam Numbers Through Verification Hubs
Verification hubs, by aggregating validated signals from multiple data sources, provide a framework to identify suspicious activity tied to phone numbers without exposing user data.
They enable ongoing spam checks through cross-referenced metadata, rate patterns, and behavioral fingerprints.
The approach preserves privacy balance by limiting data exposure, emphasizing transparency, and relying on aggregated indicators rather than individual identifiers.
Revealing Trusted Data Without Sacrificing Privacy
In this approach, trusted data can be revealed without compromising privacy by anchoring verification signals to aggregated, anonymized indicators rather than individual identifiers. The method emphasizes verifiable provenance while minimizing exposure, aligning with data minimization principles. Evidence suggests reduced privacy risks when signals rely on collective patterns. Curated datasets and robust audit trails support transparency, empowering users who value freedom and control.
Practical Steps to Use Verification Hubs Safely
Are there concrete steps to use verification hubs safely, and what practices ensure user privacy remains intact? Verification workflows should emphasize minimal data exposure, encrypted transit, and verified sources. Implement privacy preserving techniques such as selective disclosure, local data processing, and audit trails. Regular assessments, consent-first policies, and transparent data-use summaries empower users while maintaining rigorous, evidence-based security standards.
Conclusion
A Phone Verification Hub aggregates signals from multiple trusted sources to identify spam numbers while preserving user privacy. The approach leverages data minimization and anonymized indicators, reducing exposure while maintaining verifiability and provenance. An illustrative statistic highlights impact: studies show that cross-source signal aggregation can cut false positives by up to 40% compared to single-source checks, underscoring the value of collaboration. The result is transparent data-use summaries, consent-first policies, and safer communication without compromising privacy.




